Researchers from the universities of Surrey and Birmingham, in the United Kingdom, demonstrated live a flaw in Apple Pay that allows charging any amount from a locked iPhone, without the owner authorizing anything.
The attack was reproduced by the Veritasium channel in partnership with YouTuber MKBHD, who had $10,000 debited from his own card while the phone was face down, screen off, with no interaction whatsoever.
The flaw combines the Express Transit Card feature with a gap in the specific security protocol of Visa cards.
What is Express Transit Card
The Express Transit Card is an Apple Pay feature created to make it easier to use your phone at subway and bus turnstiles.
The idea is simple: instead of unlocking the device every time you pass through a gate, the iPhone automatically detects the transport terminal signal and authorizes the payment instantly.
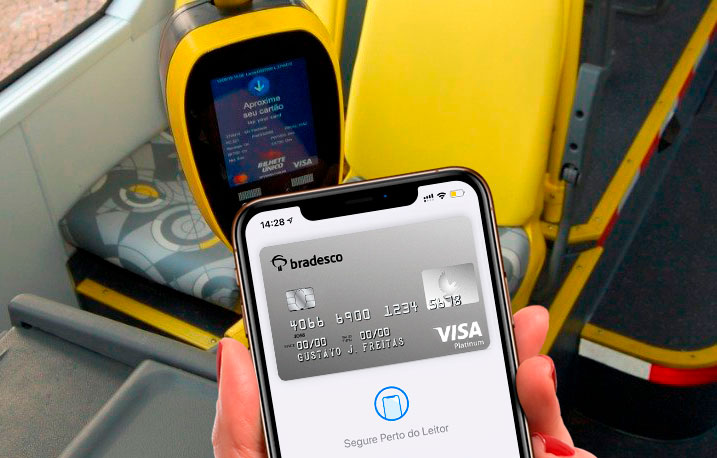
No Face ID, no passcode, no action required from you.
It’s a practical feature, and it makes sense in context. No one wants to hold up the subway line during rush hour.
The problem is that researchers discovered the exact signal a turnstile sends to the iPhone to trigger this mode.
They then reproduced that signal with their own equipment, tricking the device.
To the iPhone, it was as if it were being tapped on a subway gate. But it wasn’t.
How a $10,000 payment goes through without verification
With the iPhone believing it is at a turnstile, the first barrier is already down: the device does not ask to be unlocked.
But there are still two other protections in place.
The iPhone differentiates between high-value and low-value transactions, requiring user confirmation for higher amounts. And the payment terminal, upon receiving the response from the iPhone, checks whether that confirmation actually took place.
The researchers bypass both.
They intercept the data transmitted over the air between the iPhone and the terminal and alter two bits of information: one that classifies the transaction value as “low” (even though it is $10,000) and another that tells the terminal the user has already confirmed the payment (even though nothing was done).
The bank receives everything as valid, approves it, and the money is gone.

Why this only happens with Visa
This attack does not work with Mastercard.
The difference lies in a security layer that Mastercard requires in all transactions: a digital signature between the card and the terminal that makes it impossible to tamper with the data without being detected.
If anyone alters any information along the way, the signature won’t match and the transaction is rejected.
Visa only requires this layer in specific situations, such as when the terminal is offline (a common case in underground subways).
The researchers ensure the terminal is online during the attack, and as a result Visa simply does not trigger the more robust verification.
The vulnerability exists in this specific combination: iPhone with Express Transit Card set up using a Visa card.
It also does not work on Android. Samsung devices, for example, in transit mode only accept zero-value tap transactions and charge the full amount later.
A terminal trying to charge $10,000 in one go would be immediately rejected.
What Apple and Visa said
Apple stated that the issue lies with Visa.
Visa acknowledged the possibility but downplayed the problem.
It claims that large-scale fraud is unlikely, that it has effective detection systems, and that if it does happen, consumers can dispute the charge and will be reimbursed.
The position of both companies today is exactly the same as in 2021, when the vulnerability was first disclosed. Four years, zero changes.
What makes Visa’s response particularly hard to accept is that the technical solution already exists and is already in use. Mastercard solves this by requiring a digital signature between the card and the terminal in all transactions, making it impossible to tamper with data in transit without detection.
Visa could do the same. This is not a technical limitation, it is a choice.
Instead of closing the gap, Visa points to the low rate of contactless fraud (2 cents for every $100 in in-person transactions) and its reimbursement policy as a sufficient response.
But this shifts the burden to the consumer: noticing the unauthorized charge, contacting the bank, disputing the transaction, and waiting.
Anyone who wakes up with $10,000 missing from their account will feel the impact before any refund arrives.
How to protect yourself
The most direct solution is to disable Express Transit Card on your iPhone.
To do this, go to Settings > Wallet & Apple Pay > Express Transit Card > None.
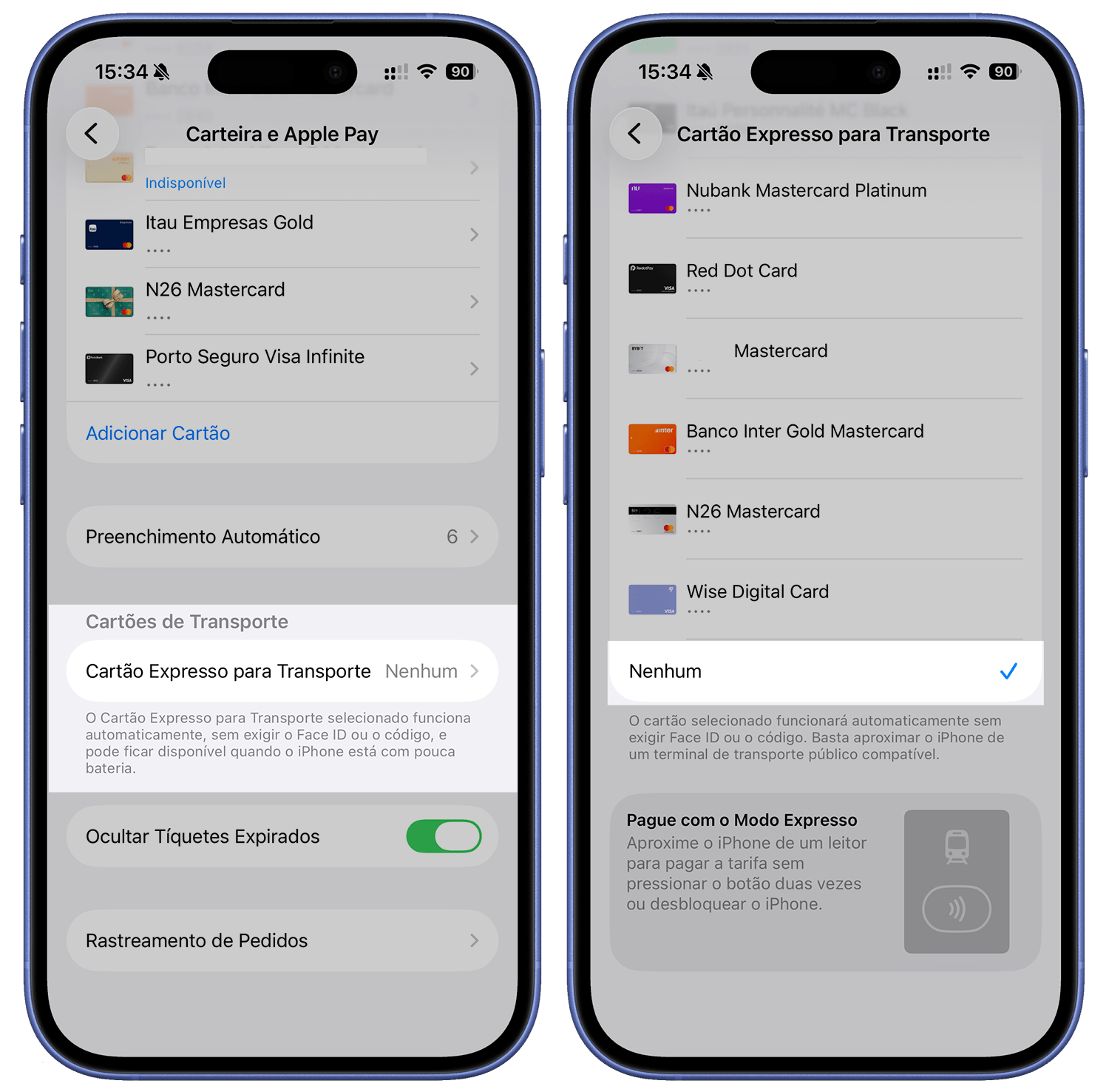
It’s worth checking because this feature is automatically enabled when you add a compatible card to Apple Pay, often without you noticing.
If you use Apple Pay with Mastercard only, there is no risk from this specific vulnerability. But if you have a Visa card set as your transit card, it is recommended to act now.
The full Veritasium video, with the live demonstration and detailed technical explanation of how the attack works, is right below.